0:00:05 – (Matt Widdoes): Welcome to Growth@Scale. I’m your host, Matt Widdoes. This is a podcast for leaders who want to bring sustainable, predictable, scalable growth to their businesses. Every episode, I sit down with world class growth experts across product marketing, finance, operations, you name it. The hope is that these conversations will give you real, actionable advice for building and sustaining company growth.
0:00:26 – (Matt Widdoes): Our guest today is Khelan Bhatt, CISO and VP of IT at Fabfitfun.
0:00:30 – (Matt Widdoes): Khelan takes us through the basics of cybersecurity for new and established companies.
0:00:32 – (Matt Widdoes): We talk threat detection, data handling, and the true cost of a cyber attack for your company.
0:00:39 – (Matt Widdoes): Enjoy. Welcome to the MAVAN podcast. I’m Matt Widows, your host and CEO of MAVAN.com. And today, we’ve got Khelan Bhatt on the podcast. Khelan, welcome to the podcast.
0:00:55 – (Khelan Bhatt): Thank you, Matt.
0:00:56 – (Matt Widdoes): Thank you. Yeah. Could you introduce yourself? Tell us a little bit about what you do, where you work, and the things that you’ve done in the past?
0:01:01 – (Khelan Bhatt): Love to. Really excited to be here, Matt. So I’m Khelan. I’ve been in the information security industry for my entire career. Almost 20 years. Prior to being CISO Fatfit Fund, I was deputy CISO at Gap, Inc. The parent company of Gap, Athleta, Old Navy, Banana Republic, and a bunch of other brands. Before that, I was global director of network and cloud security for Anheuser-Busch InBev. And before that, I spent a number of years in various security roles, as an engineer, as a product manager, as a director of product. Always centered around cybersecurity, information security.
0:01:31 – (Matt Widdoes): Cool. And what is a CISO? What do they do?
0:01:33 – (Khelan Bhatt): So a CISO’s role is really to be the top person at an organization responsible for information security, cybersecurity, and sometimes also privacy matters. The CISO is equivalent to any other C level executive, where, whether it’s a CFO, CMO, Chief People Officer, they have complete and final oversight over guiding an information security program for a company, making sure that all the different safeguards are in place, that a company’s vision and mission is aligned with best practices in enforcing security.
0:02:05 – (Matt Widdoes): And it’s kind of a constant changing threat. It’s like cat and mouse. As soon as you kind of shore something up, there’s another.
0:02:12 – (Khelan Bhatt): Yeah, definitely. We have job security in that regard. Wack-a-mole. Yeah. I think I like to take an analog from medicine and from health, that there’s always some new and emergent threat, that there’s always some infections going around, people are always getting sick, but it’s about hygiene. It’s about improving the culture of wash your hands and cover your mouth when you cough. It’s similar, but you’re doing it for a company and you’re doing it with the business in mind and in spreadsheets, you’re doing in spreadsheets and you’re definitely doing a lot of slides and kind of things like that. You’re both managing up to the executive level to the board and also managing down across your organization and really kind of pushing the culture of security at a company because that consistently is the biggest job. The technology part is a little easier. It’s the culture and the people, which is always harder.
0:02:59 – (Matt Widdoes): I assume that includes things like internal phishing attempts and trying to get people to click a bad link.
0:03:05 – (Khelan Bhatt): Yeah. Depending on the maturity of an organization, you could have substantial internal checks, insider threat programs, things like that. So at various stages in my career have worked in this role for different companies and seen, we’ve done a lot, but at bare minimum, yeah, seeing who clicks on a link that you send out to test, that’s a good measure of how susceptible you are.
0:03:25 – (Matt Widdoes): That’s funny. At a previous company of mine, we do kind of an onboarding, and it’s usually people flying from all over the country into one space. And as part of that onboarding, security team comes and talks about various things. How do you enter the buildings and just various processes. And then they talk about phishing. There’s a whole segment on it. And they say, in your first couple of weeks on the job, we are going to send a phishing test.
0:03:45 – (Matt Widdoes): And despite telling you that some people in this room are still going to click on it, and they do and they don’t name and shame, unfortunately. But it’s just funny how even when it’s told to you in advance, it’s just a constant threat. We were actually attacked, funny enough, at MAVAN where we had received some text messages. Various people on our team got texts all saying, hey, it’s Matt. I need you to go to the, I’m with a client right now. I need you to go to Target and get me gift cards.
0:04:13 – (Khelan Bhatt): Yeah.
0:04:13 – (Matt Widdoes): And people were like texting me, like laughing about it. So I think a few of our people wasted time with them and they were like, oh, hey, I’m at target, boss, what do you want?
0:04:21 – (Khelan Bhatt): That means your immediate team have that cultural awareness, that level of understanding that, oh, your boss would never text them. But imagine a larger organization order of magnitude larger where there’s thousands of employees and you just may get a text from some higher up.
0:04:36 – (Matt Widdoes): Yeah. Well, when you’re doing it in mass. And it costs the same to send it to a trillion people as it does to send it to ten. It’s like, what do you care? I think oftentimes these phishing scams and various email scams really are targeting. I’ve heard before, like those Kimmer were called, but the Nigerian prince scams, you know how those oftentimes have like typos. They’re very obviously not written by an English-first writer.
0:04:59 – (Matt Widdoes): You may know this or have heard of this, but I’ve heard that they are intentionally written poorly so that they weed out anybody with any sense of what might be happening. And it just is better for their funnel to just get people to not try and click. They’re trying to get to the lowest common denominator as fast as possible, which is very sad. But they’re like, no, that’s like on purpose that we misspell words.
0:05:18 – (Khelan Bhatt): Essentially, they’re segmenting their money very well.
0:05:21 – (Matt Widdoes): So I’m curious. At MAVAN, we spend a lot of time thinking about bringing in the right person with the right skills at the right time and most importantly, for the right amount of time. This is a big role, and I think traditionally people associate it with really big companies. But there must be things that companies can do in the early days, right? Whether it’s two founders in a garage, maybe not that point. I’m curious, actually, at what point can people start working on it? But what does this function look like? Less about the title, but like the function of security and information security broadly, what does that look like in the earliest days of a company, however, you want to define that all the way to a Series D or large public company like Google or something like that. What does that kind of typically look like for this function?
0:06:03 – (Khelan Bhatt): Yeah, so it’s a great question. And security is something that I believe you need to think about from day one, really, in this modern era of how we do business, especially if you’re doing anything with e-commerce data, which requires extra to protect. If you think about usually the very first person in a company is the CEO, the founder, and they’re wearing all the hats. Business to technical, to sales, to marketing, to people, to everything. And CISO is much farther down the list, I’d argue just kind of anecdotally, it comes well after CFO. And initially it’s just thinking about the basics. How do I password protect whatever assets I have if I’m a cloud native company?
0:06:40 – (Khelan Bhatt): How do I figure out if something is going wrong to come in and remediate something. So the same person typically that does kind of the IT support initially is going to be doing the security function that quickly gets complex. So I’ve seen in really early stage seed and even up to Series A companies, the CTO is serving the function of CISO. They’re responsible for embedding security, whether it’s engineering that into the platform, whatever you’re building to managing the keys to the kingdom, your root passwords and things like that. And that’s actually appropriate because typically the technical folks, founders of the company or early employees, they had that right mindset from a technology perspective of these are the basics, this is what we have to do. So hopefully that kind of lets you understand the early days, what I’ve seen shift at a certain revenue size, let’s say anecdotally $20, $30 million ARR you start specializing in. I want to bring in security professionals. You won’t call them the CISO. Your first security hire is in fact going to be probably an engineer who’s already on the payroll and now doing things that are specific to security, but that person will be kind of dubbed the ‘head of security’, and you’ll just kind of continue from there. Now, the exception is if you get breached, there are things that can accelerate. If you’ve had a cybersecurity incident, then the stakeholders and the leadership will probably make a determination that we need to dub somebody Head of Security officially with that title. So that’s traditionally how it’s been. But increasingly, because security incidents and cybersecurity and privacy have become so important and made front page news, you’re seeing your business partners and your investors ask, well, who’s your CISO? Who have you designated?
0:08:16 – (Khelan Bhatt): Cyber insurance is becoming a much more common thing. And any cyber insurance application you fill out will ask, what’s the name title of that individual? How many other people reports that individual or works in that security function? And so it kind of forces you to really think about a structure around security and make it much more formal of a department or function within a company.
0:08:38 – (Matt Widdoes): Mentioning that, I guess it sounds like early days, there’s many people trying to do it, and maybe early days, it looks like let’s use two factor authentication, let’s use a password management tool, maybe single sign on or things like that, to kind of generally have some form of security. And then as databases grow, certainly the attacks, from my experience, follow the money, right? So you look at things in the marketing world, at least from, say, like affiliate marketing, where people are getting major payouts. We had dealt with this a lot when I was in real money gaming in the fantasy sports space, where we offer a $120, if you can, for anybody that sends us somebody that deposits $10, we will give you $120-200. Obviously, if we’re offering up a $200 bounty for a $10 deposit, you could just take it from the bounty. Right? So it’s like instantly profitable, $190, if you can do that. So when people are kind of attacking, I guess maybe it largely probably comes down to they want credit card numbers.
0:09:34 – (Matt Widdoes): What are some of the things that people are trying to get? They want credit card numbers, they want addresses, they want email lists. What is it? Are they trying to hack into your financials? What does that typically look like? Maybe I get that there’s lots of things, right? It all boils down to various data and who values what.
0:09:54 – (Matt Widdoes): But what are kind of the most common top five things that people are trying to get industry wide?
0:09:55 – (Khelan Bhatt): Yeah. So I’ll speak from a bias of having worked a fair bit in ecommerce. So credit card numbers are incredibly valuable. If you, as a hacker, as a cybercriminal, can embed yourself in that site or app or some back end system where you’re essentially virtually skimming things, then that’s incredibly valuable. And there’s a big and liquid market for reselling stolen credit card numbers.
0:10:17 – (Matt Widdoes): Where do I go to buy those numbers?
0:10:20 – (Khelan Bhatt): The dark web.
0:10:23 – (Matt Widdoes): What’s the address for the dark web?
0:10:25 – (Khelan Bhatt): By the time they get to you, they’ve probably been sold and resold so many times that they’re worthless.
0:10:30 – (Matt Widdoes): But it’s kind of like lead gen, honestly, we see that a lot where you fill out a form online and then suddenly your phone won’t stop ringing and you’re like, now I’m down to the bottom of the barrel of the guy who bought it three months later.
0:10:40 – (Khelan Bhatt): Yeah, it’s probably an exact great analog, but credit card numbers are huge. PII, personally identifiable information that can be used. It’s usually packaged and then resold again on the dark web. So that’s really valuable. Trade secrets and IP. If you’re a high tech organization, that’s designs and source code and things like that, that’s incredibly valuable.
0:10:59 – (Matt Widdoes): Super valuable.
0:10:59 – (Khelan Bhatt): Super valuable. And I’d say infrastructure itself is valuable. So if I had access to your AWS VPC, I could resell that, or I could use it. I can set up crypto miners and just make money directly that way and just plug away and you’ll get a huge bill. I could use that capability. Having a foothold in your infrastructure to apply targeted attacks, denial of service attacks against people, that I can get paid for attacking other people. I can set up a botnet. You can also use that infrastructure to send out spam, malicious messages and essentially use that infrastructure as a basis for a bigger business.
0:11:33 – (Khelan Bhatt): And then there’s much more nefarious things about nation states and kind of hacking outfits that are aligned with those who want to do much more harm than just pure cybercrime, that they want to take down critical systems and things like that.
0:11:46 – (Matt Widdoes): I’m curious. I’m going to ask you to venture a guess. Would you guess that the two industries, the kind of cybercriminal industry and the CISO industry generally, right. Anything as it relates to information security are equal in size or that one is bigger than the other? Because it sounds like a big business.
0:12:01 – (Khelan Bhatt): Mean, you know, when you say kind of information security information… No, no, I definitely think know there’s a lot of numbers out there, but Gartner and folks like them, they release these figures, which I wish I googled it before I talked to you, but there are many hundreds of billions in size. So companies spend hundreds of billions of dollars annually on information security. A business is not going to spend that money unless there is a cost.
0:12:26 – (Matt Widdoes): A payback doing that.
0:12:27 – (Khelan Bhatt): Yeah. So I would argue that it’s not even a payback. It’s basic. We’ve been wounded, we need to heal, we need to back ourselves up. It’s definitely been a, by and large in the industry, it’s definitely been an area where reactive, not proactive in spend.
0:12:41 – (Matt Widdoes): So it sounds like then the attack side is probably higher in value because if nothing else, because there’s some attacks getting through that aren’t even being accounted for, then you have to hire all the staff, you have to pay for all the tools. This is constant work. So it’s a big deal. And I guess also because you kind of follow the money in these types of situations, there’s long tail value in smaller companies that are doing $2 million in revenue or whatever, but really the value probably for most hackers because the cost of getting in is probably similar in some respects. Although the larger companies are going to have way more defense. Right. It’s for sure going to be way more expensive to hack into Google than it is to a company doing $420 million in ARR. But the size of the prize is much larger. So I guess they kind of maybe Red Queen’s Race move into.
0:13:23 – (Khelan Bhatt): Yeah, I would say maybe… You would imagine. But there’s also a concept of attack surface. So Google has a vast footprint yes, they have excellent security controls, but in, what is it? 2009, the reportedly Chinese based hackers were able to gain foothold into Google’s infrastructure, and Project Aurora was this kind of well known series. So if you’re smaller, you’re maybe not on the radar of the Chinese government, but just kind of your earlier point, doing some quick research while you’re talking.
0:13:55 – (Khelan Bhatt): $3 billion in cryptocurrency has been stolen so far this year. This is from this year? Yeah, just in this year, some blockchain analysis released this figure. And just this year, just in crypto, we’re not talking about costs of fraud, in other wire fraud and hacking an actual bank and stuff.
0:14:14 – (Matt Widdoes): Right.
0:14:14 – (Khelan Bhatt): So that’s a big number just for three quarters of the year, and it’s already bigger than it was in 2021, so it’s definitely accelerating. And some firms and some industries, they got to hire a CISO from day one. They have to think about security. So any sort of cryptocurrency, fintech, or heavily regulated type of a company, or if you cater to those companies, you’re going to want to think about security from right when you hired your first employee.
0:14:41 – (Khelan Bhatt): Yeah.
0:14:41 – (Matt Widdoes): Well, I guess the silver lining on that is that $3 billion so far this year. But that $3 billion is now only worth $9,000.
0:14:50 – (Khelan Bhatt): The poor hackers, they lost so much.
0:14:52 – (Matt Widdoes): Yeah, exactly. Nobody thinks about how much money the hackers have lost in the market. This is coming from somebody who is moderately long on crypto, so no offense to any crypto listeners out there. So I’m curious, what are the most common questions you get asked that sometimes reveals interesting things?
0:15:09 – (Khelan Bhatt): It’s just, where should we start? What should I do first?
0:15:12 – (Matt Widdoes): Is essentially my questions today.
0:15:16 – (Khelan Bhatt): Where should we start to think about security? And my answer is, there are frameworks out there. I personally, at my current company, we prescribe to the NIST cybersecurity framework, which is very well known. There’s ISO 27,001, there’s different standards depending on where you are in the world. But I think the answer is, pick a standard. Start with that, because lots of people have thought about the different pillars of security, the different controls, and then just map that to your business.
0:15:42 – (Khelan Bhatt): Anytime I’m talking to anyone, whether it’s in the sea level or just working with a third party or an engineer who’s really down in the trenches turning the screws, I always start with, what is the mission of our company or organization? Because I use that to build common ground, but also to create some guardrails around the scope of what are we trying to do? Are we selling widgets? Are we performing robotic surgery on infants?
0:16:04 – (Khelan Bhatt): Is this a government project? And based on that, you’ll know. Essentially what you’re doing is you’re kind of doing something called a threat model, but you’re not doing it for a particular application or a device. You’re doing it for the entire company. Like, let’s build a threat model and think about what’s valuable. Who are my potential attackers? Where’s the threat coming from? And sometimes the threat is coming from inside. People don’t realize that it’s somebody in accounting who has too much control or has admin rights on an engineering tool just because they switched roles or when their account was created, it gave them admin to everything, and they fat finger something. So I would look at it from that perspective. Start with a standard like, niche cybersecurity framework, and then build a threat model. Typically you’re going to look at things like identity and access management infrastructure or network access, application or product security and detection and response. Those are just to name a few.
0:16:54 – (Khelan Bhatt): Those are good places to start.
0:16:56 – (Matt Widdoes): And I’m curious, it’s funny you mentioned the accountant that has access. Something that we see a lot, and certainly I’ve seen a lot in my previous roles, is dealing with large swaths of data, of internal data that’s been scrubbed of PII. But I’m working as a marketer with external partners. Maybe we know segmenting, maybe we are sending lists for suppression so that we’re not targeting certain people that are already in the group. I’m curious, in this kind of post IDFA world, with higher governance around data warehousing and security, what does that mean for data handling, and particularly for marketing teams who may need to share some of this data with external partners, any considerations that marketers need to have as it relates particularly to running campaigns globally, but just in general?
0:17:40 – (Khelan Bhatt): Yeah, I mean, first of all, I’ll just say everybody’s still trying to figure out post-IDFA world, it’s a new way of doing business, and at least it’s a level playing field. But we’re still figuring out how to tackle targeting data in this world. As far as dealing with marketing teams, data handling and third party, they’re typically in an organization that has any sort of maturity. You want to create something akin to a security and privacy review.
0:18:05 – (Khelan Bhatt): This is something that is required for sanity. It sometimes could be mandated by regulation by your industry, but it’s a good idea because that security and privacy review, just like a legal review before you sign a contract, it’s important to understand what type of data that we’re talking about. So you want to classify the data, then you want to understand who are the data handlers and the data processors and make sure everyone is aware that this is happening. Because I’ve found sometimes the business, let’s say the marketing team or the data science team in a rush to solve a business problem, they are not aware that, by the way, we agreed to all these other things, we’re working with this third party, and they have this wonderful analytics engine and they do all this kind of cross referencing and deduplication and sanitizing. But by the way, we just gave them our prized possession, like our customer list, for example, and so making sure everybody’s aware of that.
0:18:55 – (Khelan Bhatt): I wouldn’t say it’s a no go from a security and privacy perspective, but
surfacing these sorts of things are really important so that you don’t have any surprises later, like, oh, you have a copy of my data retention and usability of that. That’s really important. And I’d say this is where it confounds more privacy and security minded folks, because you can have something written in a contract with a third party saying, we’re giving you this customer data, you’re going to help us target more effectively if you’re going to send out email blasts or whatever. But do you really trust their systems? Do you really trust that they are going to scrub that data or sanitize it or even store it in a way that is up to your standards? And that’s where folks like myself ask those hard questions of those third parties. So we’ll look for maturity. Do they have a published security and privacy framework? Do they have some white papers? Do they subscribe to, for example, something like a NIST CSF? Do they have a soc two type two report?
0:19:46 – (Khelan Bhatt): What is there under the hood? And typically we’d ask them questions, send out some sort of a questionnaire and get some input back, and you can tell who’s at least somewhat serious about security based on who’s doing the response. If they have a CISO or VP of Security or an equivalent privacy side, then you know that they’ve made that investment, at least an initial investment. So probably that person is doing their job.
0:20:10 – (Khelan Bhatt): But there’s other things I’d look at in terms of, so things like that I’d look at to get a sense of who’s a quality partner to do business with and how mature they are.
0:20:19 – (Matt Widdoes): And so on that same topic, what are a few things that you wish marketers better understood about data, so they’d stop making your job so hard. Maybe you don’t want to entirely get rid of it, but what are some kind of things, from junior media buyers, to people working with third party contracts, to people even just advertising on major platforms, what are any things that you wish they’d stopped doing or that they’d start doing?
0:20:43 – (Khelan Bhatt): The very first thing I’d wish marketers, or anyone really working with large chunks of data, would do first is bring security and privacy. Whoever that head is, whether it’s a CISO or somebody much more junior, bring that person along for the journey early in the process. If you’ve already signed a contract with someone, it’s too late now. We’re the bad guys. We have to come in, we have to stop things. Sometimes we’re not even empowered to do that. So it really slows things down. And the likelihood of your business partner actually building something in after you’ve signed the contract is much less. They’re not as incentivized to do it. So bring us in early like you would legal, because you know legal will bring the hammer down on you if you don’t. So bring us in right at the same time of contract negotiation. That’s the first thing I wish everyone would do, but particularly in the realm of marketers and people working with data, I think the second thing is, understand that data is extremely easy to duplicate. It’s extremely easy to lose control of that data. So any single copy just increases that kind of risk. Right. It dilutes the controls, essentially. It creates headaches from deduplication later that maybe are going to be interesting for the marketer, but it’s extremely easy to copy. But that is very risky from a governance perspective. Maybe the third thing I’d want to talk about is how granular can you get in defining the different roles and responsibilities of access to that data?
0:22:02 – (Khelan Bhatt): Does every single person need read/write access and admin access to the data? Can most people just be readers? And not only just readers, but can we really give granular control, saying, these are the types of fields, these are the columns, these are the rows, even that we’ll give you access to, because this is your function and have that be really ephemeral? There’s technology that does that, but we need you to really think about that, because from a security perspective, we’re just engineering the controls and guiding you. You’re the ones telling us, this team over here needs to target everyone with a dog in this zip code.
0:22:35 – (Khelan Bhatt): But does that mean that they also, can we hide fields about their income and things like that just as an example. As a terrible example.
0:22:43 – (Matt Widdoes): That makes sense. Well, yeah, because you don’t need, I mean, for digital marketers, they’re almost never going to need the last name. Right. And for people sending mailers, they’re never going to need the email address. Right. For people sending physical mail. So I think that all tracks. Yeah. And you’ve worked at some pretty large corporations. You mentioned gap and must, as you get bigger, generally, companies are operationalizing processes around data and security.
0:23:11 – (Matt Widdoes): What kind of best practices exist as companies are scaling that should be considered to ensure they’re not leaving threat vectors open and leaving themselves open to the punch?
0:23:24 – (Khelan Bhatt): Well, let’s start with just kind of the data perspective. It’s been invoked to create a data lake because data together is more valuable than data siloed, and it’s also better from a governance perspective. So I’ve seen that trend, especially for AB and BeV and gap and companies of that size and scale. Let’s get our data lake, and we can run all these analytics and data science and we can create ephemeral access and just do all these amazing things with all that data in one place, run models. So that’s been one trend, and I’m generally in favor of that because it helps people like me do our jobs a little bit better.
0:24:01 – (Khelan Bhatt): The goal is getting to that data lake and making the investments to institute controls over that. More broadly speaking, I’d look at companies as they’re growing in size and scale and maturity. To really go back to the beginning question we asked when you were a startup and when your company was just still thinking about security, and it was, what’s that framework? How does it work for us now at this level of maturity? So let’s assess, is it still serving.
0:24:26 – (Matt Widdoes): Us kind of thing, or how does it kind of evolve with our needs?
0:24:31 – (Khelan Bhatt): Yeah. How have we matured against this particular framework, against this standard? And that requires an assessment just kind of like an audit once a year and sometimes even much more periodic than that. We run informal quarterly assessments. And other places I’ve worked, we’ve done formal quarterly assessments, and sometimes third parties, definitely. If you’re an e-commerce like PCI (Payment card industry), they mandate things like that.
0:24:56 – (Khelan Bhatt): If you’re in healthcare, that industry will mandate that. Let’s get this assessment done every quarter, and that’ll tell you how you’re maturing. But any well run organization is going to surface that, and that’ll be a board level slide you may not get time to speak on it, but it’s definitely going to be in that board that’s created every quarter. And the board’s going to want to look for progress year over year and identify those one or two big risks, because what they don’t want is the surprise in a month. That’s, oh, our entire facility was shut down because of a ransomware outbreak.
0:25:26 – (Khelan Bhatt): And that happened because all the pcs were Windows 98 and weren’t running antivirus, and we had no firewall. They want to know in a bullet that this is a risk, that somebody called it out, and it’s a risk because we didn’t make that investment and because there wasn’t money allotted to that. They want to know that.
0:25:45 – (Matt Widdoes): And then taking a step back, where do you see kind of the overlaps with security and growth? We approach growth at MAVAN from many different angles. This is a prime example of it and how we think about growth holistically. What are kind of the talking points you feel like early stage companies should understand about security as it relates to growth, or even like late stage. I think generally it doesn’t necessarily have to be focused on early.
0:26:08 – (Matt Widdoes): What are some of those things that overlap?
0:26:11 – (Khelan Bhatt): I would challenge a company at any stage, but certainly early growth stage, to think of security not as a roadblock, which it’s kind of inherently how you think about it. Like, oh, they’re putting up hurdles and they’re slowing us down. That’s traditionally been the case. But if you talk to the best run early stage companies, the ones that you want to do business with, they’re sharing very publicly and early what they’re doing for security, they recognize that this is why you’re hesitant to do business with them. So if you are that third party that requires your customers to share data with you, or if you are that third party that is providing a critical service, and it means integrating deeply between your infrastructure and your customers infrastructure, know that your customers are going to look for certain clues early on, and they may weed you out if you are missing that even on your website and in your marketing collateral before you even engage. Things like your sock two type, two attestation, whether you have a bug bounty program, whether you have somebody on your leadership team that deals with security and privacy, those are things that I look for when I’m doing a cursory review, even before I’ve engaged with the company and your customers are looking for that. I’d say one additional thing to look at is, as you’re also thinking about how to make yourself attractive. Think about all the other things that you’re telling your customers and stakeholders that are great about you. A great place to work. You have this governance structure, you have great products, you have great support and customer service.
0:27:34 – (Khelan Bhatt): Contact me, all that stuff. You should really think about security in that same way and maybe even technically start thinking about security as a feature to increase the speed of business and let you operate at what I call the speed of trust. So did you build, if I’m integrating with you is single sign on a part of what I’m offering my customers? Because if I’m a customer of yours, maybe I want my employees to access your service through SSO.
0:27:55 – (Khelan Bhatt): Do you support that? Do you have SAML, 2-auto authentication? Do you have the latest and greatest of whatever is out there supported? Do you interface with monitoring tools, Sims and APM tools? Do you offer role-based access control so that when your customer comes to you and asks you, I don’t want everybody to have admin access, do you support that in your platform? You’re not like, oh, that’s a roadmap feature.
0:28:16 – (Khelan Bhatt): It’ll be released in Q4 of 2023. Can you do it today? Because that’ll differentiate you. So these are kind of what I would consider like table stakes. I’m a little biased here, but those are things that you can build into your offering and really advertise that and have you stand out from the others.
0:28:33 – (Matt Widdoes): It’s funny, there’s a few parallels you mentioned. One is that kind of oftentimes teams are seeing this as roadblock or not involving them early. I think that parallels very well with legal. Right? It also parallels a little bit sometimes with brand, where they’re like, brand is going to hate this, let’s just run it, particularly with paid teams. But the ability for seeing it as a feature and seeing it as a way to actually improve the overall growth of the company. The interesting thing is it’s focused, this legal brand, all of those three pillars of growth are really focused on the long term, which is super important for growth. Right. And I think oftentimes, certainly marketers, no offense to the marketers out there, but many people within organizations and even just day to day life, it’s easy to kind of lose sight of the long term compounding value of things like contracts, of things like little bullet points in a two year BD co marketing partnership can make massive differences down the line. And it’s very difficult to see that sometimes early days. So I think there’s a lot of parallels with security, legal and things of that nature.
0:29:37 – (Matt Widdoes): And it’s hard when you zoom back and you see a company that went from, they did a year one revenues of $5 million, and then they did $20, and then they did $100, and then they did a billion. You see this like exponential growth. Those little things don’t oftentimes get seen or not those little things, but these kind of ancillary long term growth things. And you could ask yourself like, well, why did they grow so quickly? And oftentimes, I think people point to marketing, they point to sales, they point to product.
0:30:00 – (Matt Widdoes): And the reality is there’s some demonstrable amount of that growth. That was because they had fast legal that got the terms that they needed and were thinking about the long term health of the company. They had people, product marketers, thinking about the long term health of their messaging and what they’re doing and testing and things like that. They had security professionals making sure that they weren’t getting attacked and that they didn’t end up in that headline. And so it’s almost like you don’t get to see the things that didn’t happen right. And that this protects so much against that as those other things do, that it’s hard to quantify right at the end. But they might have been up against another competitor who didn’t invest as much in security, who did get attacked, who did get blasted in the media, who did lose a ton of customers and business as a result of that. And nobody ever says, well, maybe we didn’t because of that effort that we put in. I don’t know if that resonates, but there’s some parallels that I draw.
0:30:49 – (Khelan Bhatt): Yeah, I think that’s a great way of looking at it. I especially like the, we’re in this not for the kind of short term. It’s not checking the box. We are building a company that has resilience and has some saying power, and we’re making these investments and these investments pay off because they make doing business with us much more transparent, much more smooth. And we’ve taken this particular thing seriously. Yeah, I think that’s an absolute great way of putting it.
0:31:18 – (Matt Widdoes): Great.
0:31:18 – (Khelan Bhatt): Yeah.
0:31:18 – (Matt Widdoes): It’s almost like you put five people who ate a nice, balanced diet with lots of salad and exercise and meditation and other things, and you put this other group who didn’t do those things and maybe went the exact opposite and ate a bunch of sugar and other awful things. And it’s like at the end of the life, you don’t know exactly how much more life and quality of life you got from some of those efforts. But, you know, it’s there, it’s visible in the data, and so it’s hard to quantify what’s the value of that? Maybe this is similar.
0:31:45 – (Matt Widdoes): So as we kind of come to a wrap here, I’m curious if you kind of picture in your mind a lot of the companies that we deal with are newly minted Series A’s, Series B’s, and we work a lot alongside their leadership teams, particularly the founders and ceos. And I’m curious, any parting advice you would give to an early stage CEO who just raised, I don’t know, $10 to $20 million? They’ve shown some early product market fit. It’s happening. They’re going to continue.
0:32:10 – (Matt Widdoes): They’re growing their team. They’re just starting to kind of scale more significantly. What advice might you give a CEO of a company in that position?
0:32:17 – (Khelan Bhatt): Yeah, I would say you should do what you can to avoid a security incident. It’s not the kind of thing you wanted to deal with. It is a significant bump in the road, and it’ll be a distraction from where you’re trying to take your company. So don’t underinvest in security, but don’t feel daunted. It’s not a binary thing where I spent nothing and now I have to spend a million or millions on a CISO and a big security team.
0:32:41 – (Khelan Bhatt): There are services out there, there’s managed service providers that will offer outsourced security, just like you can do that with legal and other functions which are not core to your business initially. So talk to your partners. There are VISO’s, consultants, you can bring in fractionally that can help guide you from the board level. There are certainly people that you can deputize within your organization.
0:33:02 – (Khelan Bhatt): You may already have the talent internally, and you can create a virtual team, a tiger team, where there’s somebody who’s technical, maybe it’s your technical co founder, maybe it’s your head of engineering who you can deputize to think about security. But you should be in those meetings at least part of that time and say, why are we doing this? Look at one of the frameworks. They’re standards. They’re free. You just go out there, pull the white paper, and they’re written in plain English or whatever language you’re operating in. Really, these are universal now around the world.
0:33:31 – (Khelan Bhatt): And just look at your business and what you know about your organization against one of these frameworks and say, what maturity level would I give myself? Am I comfortable with that maturity level at this stage of my business? Can I make a little bit more of an investment here. And by the way, the investment I make, can I talk about it to my customers and to my stakeholders, because it makes me much more attractive to them and it’s actually going to pay off.
0:33:53 – (Matt Widdoes): Great, super great advice. Really appreciate today’s call. I learned a lot. Hopefully our listeners took a number of things away. Kehlan, thank you again.
0:34:01 – (Khelan Bhatt): Thanks, Matt.
0:34:05 – (Matt Widdoes): That was my talk about all things cybersecurity with Khelan Bhatt.
0:34:09 – (Matt Widdoes): Stay safe out there. See you next time.
Book a complimentary consultation with one of our experts
to learn how MAVAN can help your business grow.
Want more growth insights?
Thank you! form is submitted
[hubspot type=”form” portal=”20951211″ id=”9c538ed2-fb12-45f1-a573-ad7953c058cc”]
Related Content
-

How Do You Build a Real A/B Testing Framework for B2B SaaS?
A functioning B2B SaaS experimentation program is built around paid creative testing and landing page optimization. Even with long sales cycles, you can know if an experiment is heading in the right direction within two weeks — as long as you track from first touch all the way through to closed contract.
-

Why Is Your B2B SaaS Attribution Broken — and How Do You Fix It?
Most B2B SaaS attribution stacks fail in one of two predictable patterns: relying solely on last-touch data, or being bolted together piece by piece until the parts no longer communicate. The fix starts with mapping every top- to mid-funnel touchpoint in sequence and tying that complete journey back to the moment a contract closes. TLDR…
-
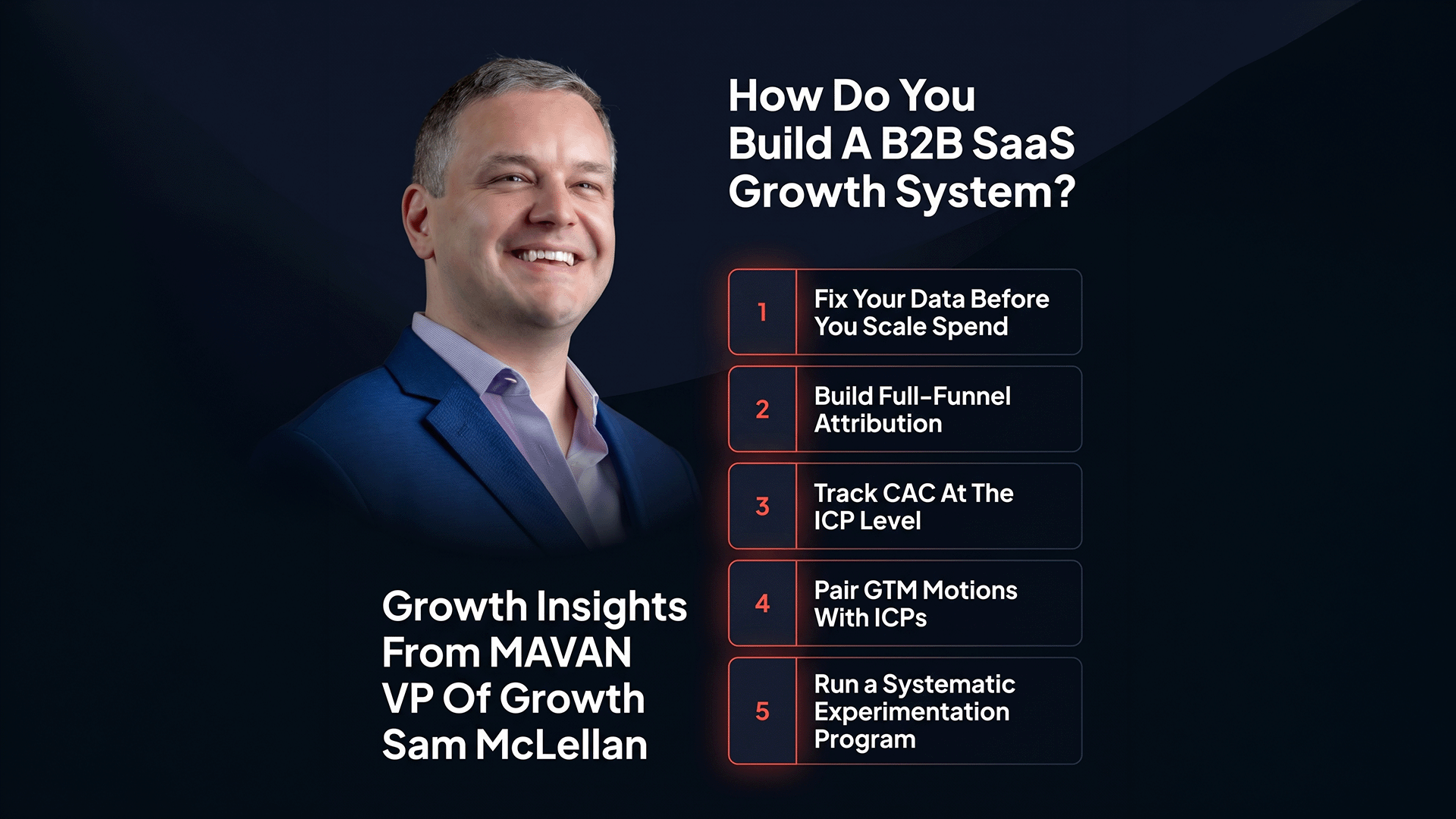
How Do You Build a B2B SaaS Growth System That Scales Beyond Founder-Led?
The fastest-scaling B2B SaaS companies are adopting measurement and experimentation disciplines from mobile gaming — including granular multi-touch attribution, ICP-segmented CAC tracking, and systematic creative testing. Companies that close that gap now are building compounding advantages that won’t be easy to replicate later. TLDR — The 10 Most Important B2B SaaS Growth Lessons Your board…